Pizza Hut DevOps Hate Me. Yet Love Me? - A Bug Bounty Story
Pre-Auth Takeover of Build Pipelines in GoCD.

| Vulnerability Operations @ Synack | Bug Bounty Hunter. Security Researcher. Wannabe hacker, sharing my thoughts on how to be successful in the cyber security space, after pivoting careers of being a decade long Sales Director.
While doing some basic recon, and digging through subdomains on various targets on different bug bounty platforms and VDP's, I came across something interesting hanging around on the Pizza Hut domain that peaked my interest.
Looking at the authentication page, I realized it was an instance of GoCD a popular CI/CD solution, in my opinion a critical piece of infrastructure because if you are looking to automate your build and release processes, a centralized CI/CD solution has access to various production environment's including private source code repositories.
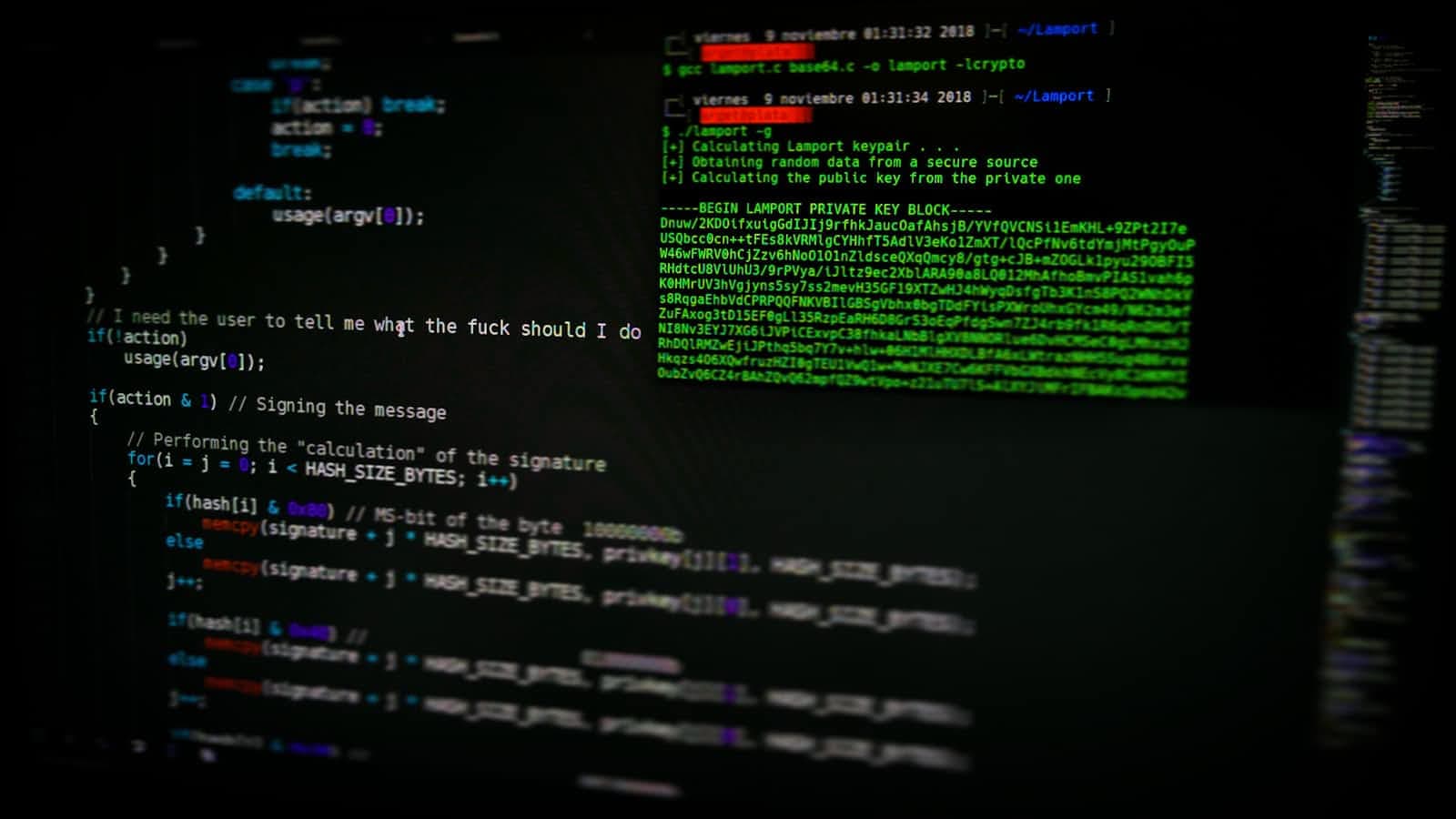
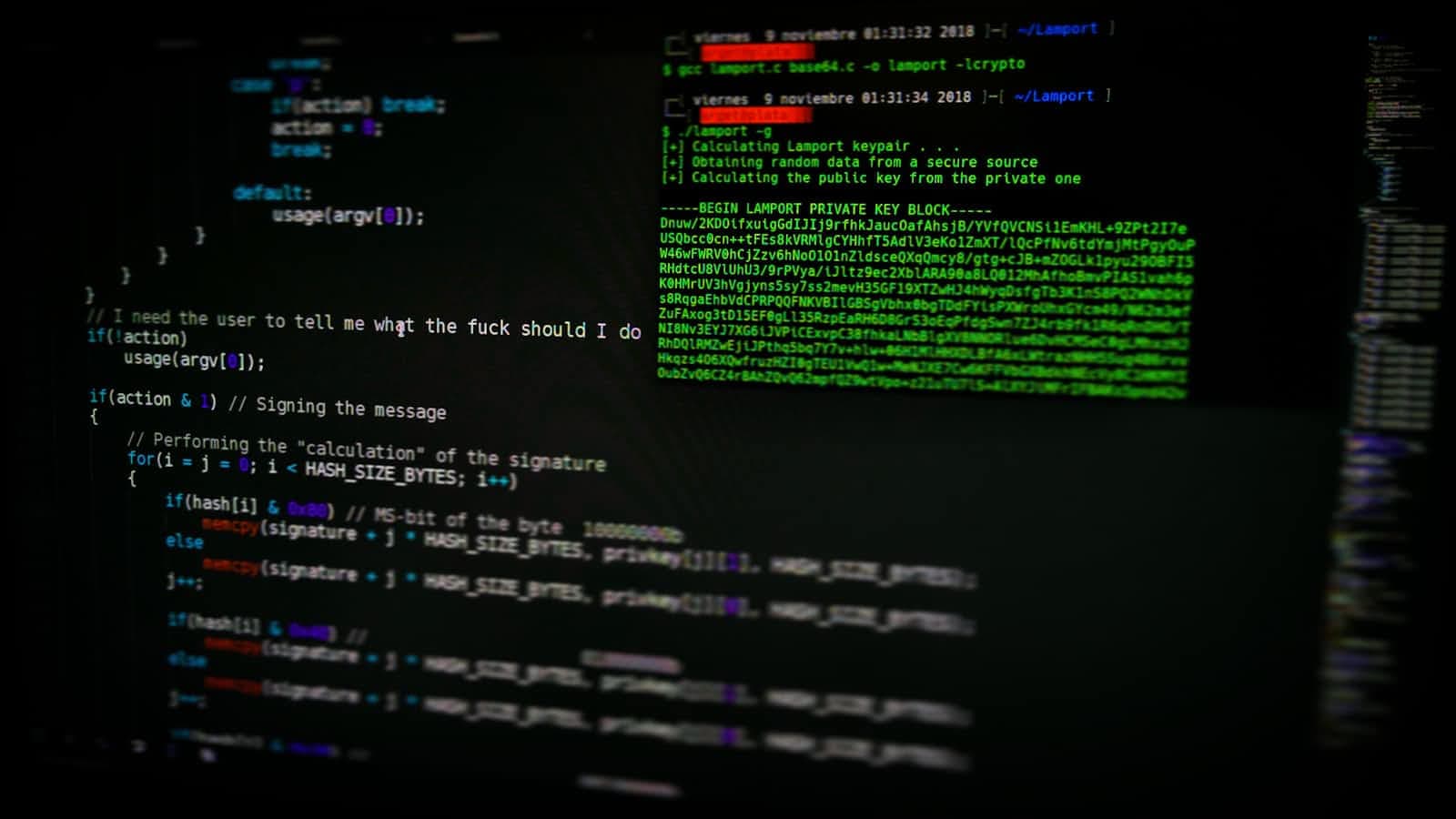
After researching more about GoCD I found that there is a vulnerability that lets unauthenticated attackers leak highly sensitive information from a vulnerable GoCD server instance, including all all encrypted secrets stored on the server (CVE-2021-43287).
**Lucky me, they were running a vulnerable version. **
All GoCD instances within the version range v20.6.0 to v21.2.0 are impacted.
The first thing I decided to check for is a known Local File Inclusion vulnerability to see if I was able to access the /etc/passwd file.
curl -v "http://[REDACTED].pizzahut.com/go/add-on/business-continuity/api/plugin?folderName=&pluginName=../../../etc/passwd"
Well that was easy, now that I know the LFI is active, let's try to grab the cruise_config file.
The cruise_config file is essentially the GoCD server configuration file that contains all the juicy secrets that we leet h4x0rs get excited for.
curl -v "http://[REDACTED].pizzahut.com/go/add-on/business-continuity/api/cruise_config"
When I received the response, I was blown away as to what I found. From various encrypted hosts, api keys, username/password combos for multiple production environments. The keys to the kingdom!
However, everything was encrypted with AES, so my excitement was short lived.
After continuing my research and looking for a way to find the encryption key that was used, I literally laughed out loud as to how simple it was to find the key. It was a simple curl request for a file in the SAME directory called cipher.aes.
curl -v "http://[REDACTED].pizzahut.com/go/add-on/business-continuity/api/cipher.aes"
After collecting myself, I decided to go through the cruise_config file and decrypt a few things to confirm that I in fact had the valid encryption key. I decided to take a peak at their sFTP credentials. I decided to use openssl to start decrypting the credentials.
openssl aes-128-cbc -d -a -K [CIPHER.AES_KEY_HERE] -iv $(xxd -p <(base64 -d <<<[ENCRYPTED_CREDS_HERE])) <<<[ENCRYPTED_CREDS_HERE]
Welp.. I now have access to EVERYTHING.
However, the impact here is far greater than having access to everything used in the cruise_config file.
There is also an auto register key that allows you to register a rogue agent to inject your code directly into the build pipelines and create a true supply chain attack, just like what happened to Solarwinds.
This wraps my first valid finding during my bug bounty hunting career!
For more information about Pre-Auth Takeover of Build Pipelines in GoCD (CVE-2021-43287), I found the Rapid7 Analysis extremely helpful: https://attackerkb.com/topics/ShpnUFlqDz/pre-auth-takeover-of-build-pipelines-in-gocd-cve-2021-43287/rapid7-analysis?referrer=search